Import-Module ServerManager
Add-WindowsFeature Web-Server -IncludeManagementTools
# You may have to add -source d:\source\sxs to the following 2 lines.
# We use a GPO that distributes that source-path to all servers.
Add-WindowsFeature Web-Asp-Net
Add-WindowsFeature Web-Net-Ext
Add-WindowsFeature Web-Asp-Net45
Add-WindowsFeature Web-Net-Ext45
Add-WindowsFeature Web-ISAPI-Ext
Add-WindowsFeature Web-ISAPI-Filter
Add-WindowsFeature Web-Mgmt-Console
Add-WindowsFeature Web-Basic-Auth
Add-WindowsFeature Web-Windows-Auth
Add-WindowsFeature Web-Dyn-Compression
# Download The following files manually and install them manually, or install with Wep Platform Installer.
# Cloud Cruiser for Azure Pack - Tenant Site Extension
# Windows Azure Pack - Tenant Site
# Windows Azure Pack - Tenant Authentication Site
# Windows Azure Pack - Tenant Public Api
# Some packages will automatically be added as Dependencies
#### Download WEB Platform Installer
# write-host Downloading WebPlatform Installer
# $source = "http://go.microsoft.com/fwlink/?LinkId=255386"
# $destination = "$env:temp\wpilauncher.exe"
# $wc = New-Object System.Net.WebClient
# $wc.DownloadFile($source, $destination)
####Start WEB Platform Installer
# Start-Process -wait -FilePath $destination
# This list of URL's is up to date 2013-11-18 and can be used for Automatic installation.
# Windows Azure Pack - Tenant Site
$source = "http://download.microsoft.com/download/8/7/2/87230A1A-D4CA-4925-B57B-8C27E5BD153C/MgmtSvc-TenantSite.msi"
$destination = "$env:temp\MgmtSvc-TenantSite.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
# Windows Azure Pack - Tenant Authentication Site
$source = "http://download.microsoft.com/download/8/7/2/87230A1A-D4CA-4925-B57B-8C27E5BD153C/MgmtSvc-AuthSite.msi"
$destination = "$env:temp\MgmtSvc-AuthSite.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
# Windows Azure Pack - Tenant Public Api
$source = "http://download.microsoft.com/download/8/7/2/87230A1A-D4CA-4925-B57B-8C27E5BD153C/MgmtSvc-TenantPublicAPI.msi"
$destination = "$env:temp\MgmtSvc-TenantPublicAPI.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
# These will automatically be added as Dependencies
$source = "http://download.microsoft.com/download/8/7/2/87230A1A-D4CA-4925-B57B-8C27E5BD153C/MgmtSvc-ConfigSite.msi"
$destination = "$env:temp\MgmtSvc-ConfigSite.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
$source = "http://download.microsoft.com/download/2/F/6/2F63CCD8-9288-4CC8-B58C-81D109F8F5A3/AspNetMVC4Setup.exe"
$destination = "$env:temp\AspNetMVC4Setup.exe"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $destination -ArgumentList "/norestart /passive"
$source = "http://download.microsoft.com/download/2/D/C/2DCA2ADA-AD18-40FC-9F2D-715977CB2FCC/AspNetWebPages2Setup.exe"
$destination = "$env:temp\AspNetWebPages2Setup.exe"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $destination -ArgumentList "/norestart /passive"
$source = "http://download.microsoft.com/download/6/7/D/67D80164-7DD0-48AF-86E3-DE7A182D6815/rewrite_amd64_en-US.msi"
$destination = "$env:temp\rewrite_amd64_en-US.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
$source = "http://download.microsoft.com/download/8/7/2/87230A1A-D4CA-4925-B57B-8C27E5BD153C/MgmtSvc-PowerShellAPI.msi"
$destination = "$env:temp\MgmtSvc-PowerShellAPI.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
# Cloud Cruiser for Azure Pack - Tenant Site Extension
$source = "https://file.ac/kLa3HIp4zBg/CloudCruiser.AzurePack.TenantSite_v1.0.3.msi"
$destination = "$env:temp\CloudCruiser.AzurePack.TenantSite_v1.0.3.msi"
$wc = New-Object System.Net.WebClient
$wc.DownloadFile($source, $destination)
Start-Process -wait -FilePath $env:SystemRoot\System32\msiexec.exe -ArgumentList "/i $destination /norestart /passive"
function Disable-InternetExplorerESC {
$AdminKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A7-37EF-4b3f-8CFC-4F3A74704073}"
$UserKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073}"
Set-ItemProperty -Path $AdminKey -Name "IsInstalled" -Value 0
Set-ItemProperty -Path $UserKey -Name "IsInstalled" -Value 0
Stop-Process -Name Explorer
Write-Host "IE Enhanced Security Configuration (ESC) has been disabled." -ForegroundColor Green
}
function Enable-InternetExplorerESC {
$AdminKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A7-37EF-4b3f-8CFC-4F3A74704073}"
$UserKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073}"
Set-ItemProperty -Path $AdminKey -Name "IsInstalled" -Value 1
Set-ItemProperty -Path $UserKey -Name "IsInstalled" -Value 1
Stop-Process -Name Explorer
Write-Host "IE Enhanced Security Configuration (ESC) has been enabled." -ForegroundColor Green
}
function Disable-UserAccessControl {
Set-ItemProperty "HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" -Name "ConsentPromptBehaviorAdmin" -Value 00000000
Write-Host "User Access Control (UAC) has been disabled." -ForegroundColor Green
}
Disable-InternetExplorerESC
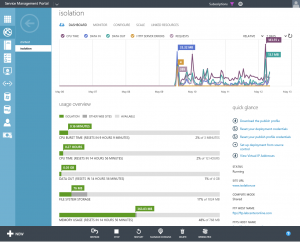
Start-Process -FilePath https://localhost:30101/