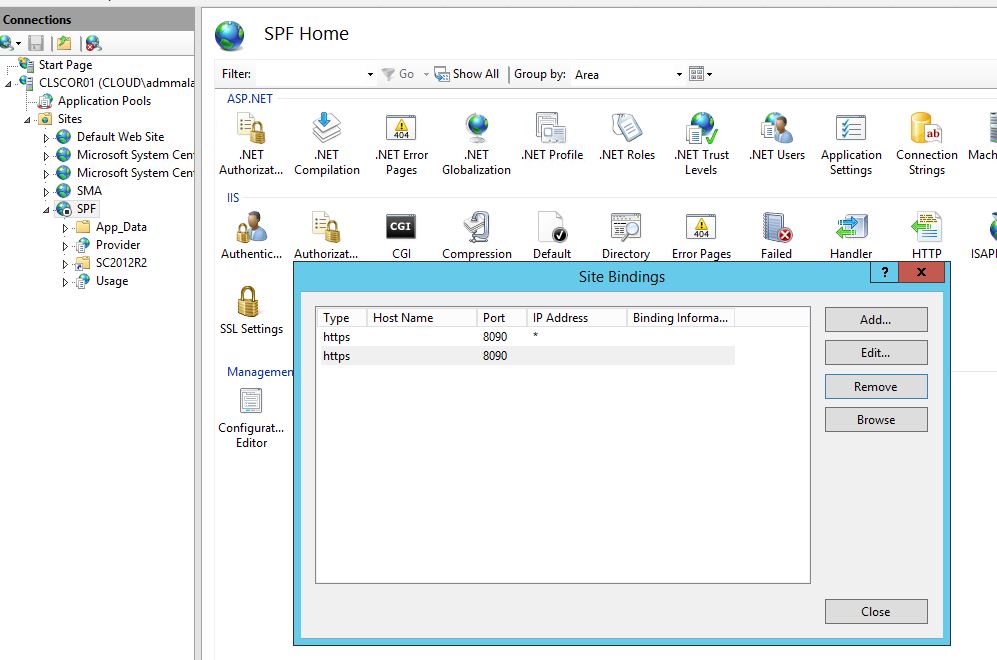
When deploying Web Application Proxy as a frontend to for example ADFS and Windows Azure Pack, or other services, the current version of Web AppProxy only supports HTTPS urls. It’s possible to use the “URL Rewrite” module for IIS to redirect users from HTTP to HTTPS. There are plenty of guides on internet on how to do that.
But I wanted to add that configuration to my WebApplication Proxy configuration script, and couldn’t find any powershell examples, so here is the script I’ve made.
It will use Web Platform installer to install the URL Rewrite module, then add the IIS Web Management tools, and in the end create a Global Rule redirecting all HTTP requests to HTTPS without the user noticing it.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
##### # Install URL Rewrite # write-host Downloading WebPlatform Installer $source = "http://download.microsoft.com/download/F/4/2/F42AB12D-C935-4E65-9D98-4E56F9ACBC8E/wpilauncher.exe" $destination = "$env:temp\wpilauncher.exe" $wc = New-Object System.Net.WebClient $wc.DownloadFile($source, $destination) ####Start WEB Platform Installer Start-Process -FilePath $destination # Wait for Installation to Complete Start-Sleep -Seconds 30 # Web Platform Installer CommandLine Tool $WebPiCMd = 'C:\Program Files\Microsoft\Web Platform Installer\WebpiCmd-x64.exe' Start-Process -wait -FilePath $WebPiCMd -ArgumentList "/install /Products:UrlRewrite2 /AcceptEula /OptInMU /SuppressPostFinish" # Add Management Tools Add-WindowsFeature Web-Server -IncludeManagementTools import-module webAdministration # Create URL Rewrite Rules Add-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webserver/rewrite/GlobalRules" -name "." -value @{name='HTTP to HTTPS Redirect'; patternSyntax='ECMAScript'; stopProcessing='True'} Set-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webserver/rewrite/GlobalRules/rule[@name='HTTP to HTTPS Redirect']/match" -name url -value "(.*)" Add-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webserver/rewrite/GlobalRules/rule[@name='HTTP to HTTPS Redirect']/conditions" -name "." -value @{input="{HTTPS}"; pattern='^OFF$'} Set-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webServer/rewrite/globalRules/rule[@name='HTTP to HTTPS Redirect']/action" -name "type" -value "Redirect" Set-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webServer/rewrite/globalRules/rule[@name='HTTP to HTTPS Redirect']/action" -name "url" -value "https://{HTTP_HOST}/{R:1}" Set-WebConfigurationProperty -pspath 'MACHINE/WEBROOT/APPHOST' -filter "system.webServer/rewrite/globalRules/rule[@name='HTTP to HTTPS Redirect']/action" -name "redirectType" -value "SeeOther" |